Standard
Penetration Test(SPT) Beginner’s Guide-2026
What a pentest actually is Standard Penetration Testing (SPT), how it works, and why it sits at the heart of modern bug bounty programs and enterprise security.
 01. Definition
01. Definition
What is a Standard Penetration Test (SPT)?
A Standard Penetration Test (SPT) commonly called a pentest is a formally authorized, systematic attempt to exploit vulnerabilities in a target system, application, or network. Unlike an automated scan that merely lists potential weaknesses, a pentest uses the same techniques, tools, and mindset a real-world attacker would use, but operates under a strict legal agreement and defined scope.
The goal is not just to find vulnerabilities, but to demonstrate their real-world impact: can an attacker actually get in? How far can they go? What data is at risk?
“A pentest answers the question: ‘If an adversary tried to breach us today, would they succeed?’ and then shows exactly how they would.”
 02. The Five Phases
02. The Five Phases
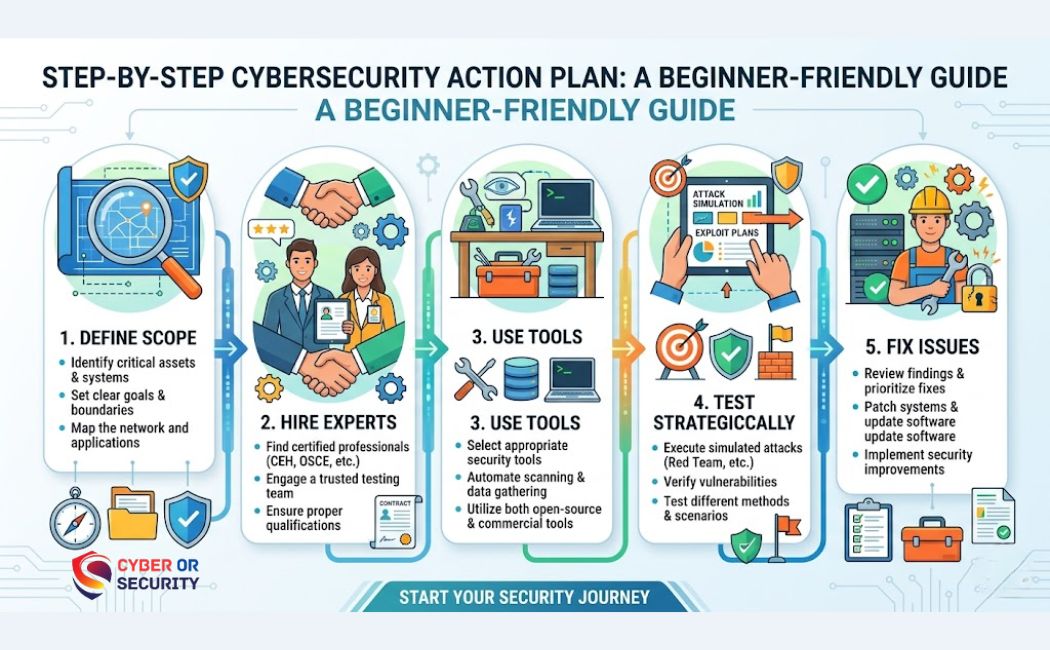
How a Standard Penetration Test (SPT) Works Steps By Steps Beginner’s?
A Standard Penetration Test (SPT) follows a well-documented methodology. Most frameworks (PTES, OWASP, NIST) agree on five core phases:
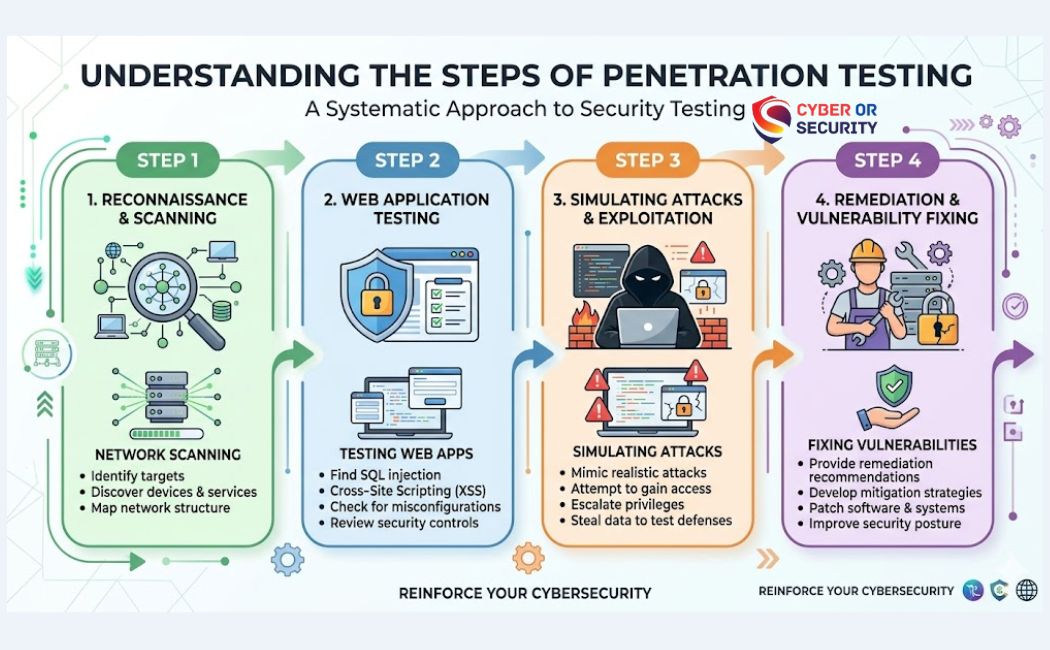
Reconnaissance
Gathering open-source intelligence (OSINT) subdomains, employee info, exposed services, tech stack without touching the target directly.
Scanning & Enumeration
Active probing port scanning, service fingerprinting, identifying live hosts, OS detection, and mapping the attack surface.
Exploitation
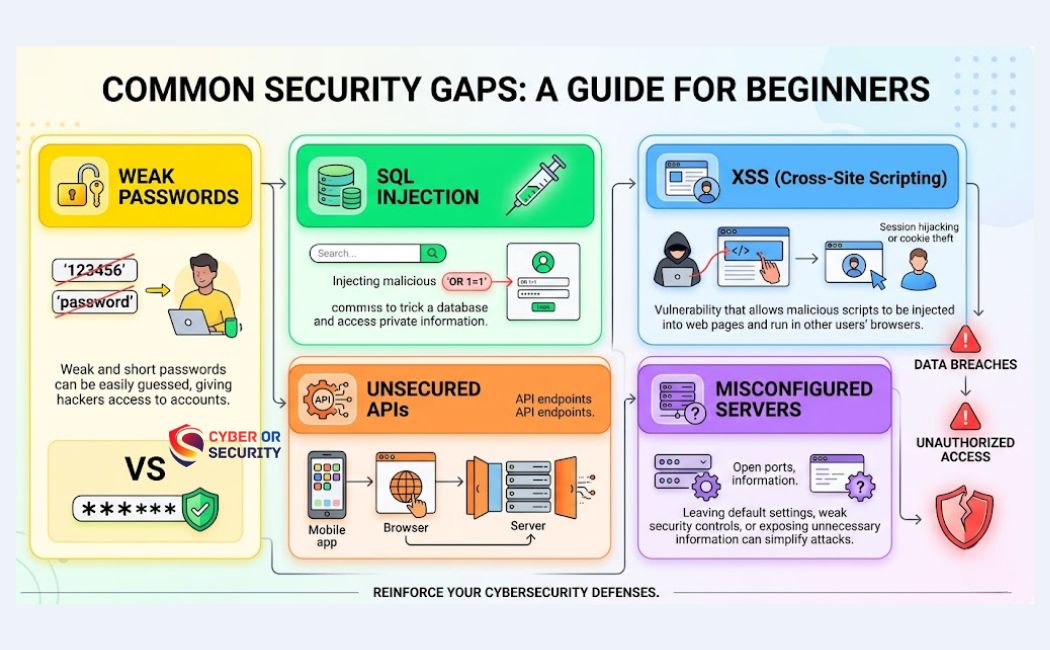
Attempting to leverage found vulnerabilities to gain unauthorized access SQL injection, XSS, broken auth, RCE, and more.
Post-Exploitation
Once inside, determining what is accessible privilege escalation, lateral movement, data exfiltration paths, and persistence.
Reporting
Producing a structured report with executive summary, technical findings, risk ratings (CVSS), and actionable remediation steps.
 03. Types of Pentests
03. Types of Pentests
Black Box, Grey Box, White Box
Depending on how much knowledge the tester starts with, a pentest falls into one of three models:
| Model | Tester Knowledge | Simulates | Best For |
|---|---|---|---|
| Black Box | No prior info — starts blind | External attacker, zero knowledge | Realistic external threat simulation |
| Grey Box | Partial info — credentials, architecture docs | Insider threat or compromised vendor | Most common enterprise approach |
| White Box | Full access — source code, infra diagrams | Thorough internal review | Dev-stage audits, compliance checks |
 04. Scope & Rules of Engagement
04. Scope & Rules of Engagement
What is in Scope?
Before any testing begins, the client and tester agree on the Rules of Engagement (RoE) the legal and technical boundaries of the test. Getting this right is critical; testing out-of-scope assets without permission is a crime.
- Target web applications
- Defined IP ranges / subnets
- APIs and mobile apps
- Cloud environments (with consent)
- VPN / remote access portals
- Third-party SaaS platforms
- Production DB (destructive tests)
- DoS / DDoS attacks
- Employee social engineering (unless agreed)
- Systems owned by others
 05. Bug Bounty Programs
05. Bug Bounty Programs
Pentesting and Bug Bounty: How They Differ (and Connect)
Bug bounty programs and pentests are often confused, but they serve different purposes. Understanding the difference is crucial for security teams, researchers, and companies.
| Dimension | Pentest | Bug Bounty |
|---|---|---|
| Who performs it | Hired firm or individual tester | Global community of researchers |
| Duration | Fixed timeframe (1–4 weeks) | Continuous / ongoing |
| Payout model | Flat fee / day rate | Per valid vulnerability found |
| Methodology | Structured, all phases | Researcher-driven, varied depth |
| Deliverable | Formal written report | Vulnerability disclosure report |
| Scope control | Tightly scoped by contract | Defined in program policy |
Many organizations run both: periodic pentests for depth and compliance, plus a bug bounty for continuous, wide-net coverage at scale.
 06. Bug Bounty Lifecycle
06. Bug Bounty Lifecycle
How a Bug Bounty Report Mirrors a Pentest
When a security researcher submits a finding to a bug bounty platform (HackerOne, Bugcrowd, Intigriti, etc.), the expected format closely mirrors a pentest finding. A well-structured report includes:
This structure directly maps to pentest report conventions the difference is that in bug bounty, the researcher must also make a compelling case for severity to maximize their payout.
07. Severity Ratings
How Vulnerabilities Are Scored?
Both pentests and bug bounty programs use the Common Vulnerability Scoring System (CVSS) to rate the severity of findings. Payouts and remediation priority follow this scale directly.
| Severity | CVSS Range | Examples | Typical BB Payout |
|---|---|---|---|
| Critical | 9.0 – 10.0 | Unauthenticated RCE, full account takeover | $5,000 – $100,000+ |
| High | 7.0 – 8.9 | Auth bypass, SQL injection, SSRF | $1,000 – $10,000 |
| Medium | 4.0 – 6.9 | Stored XSS, IDOR, CSRF | $200 – $2,000 |
| Low | 0.1 – 3.9 | Info disclosure, open redirect | $50 – $500 |
| Informational | 0.0 | Missing headers, best-practice gaps | Usually $0 (noted only) |
 08. Legal & Ethical Boundaries
08. Legal & Ethical Boundaries
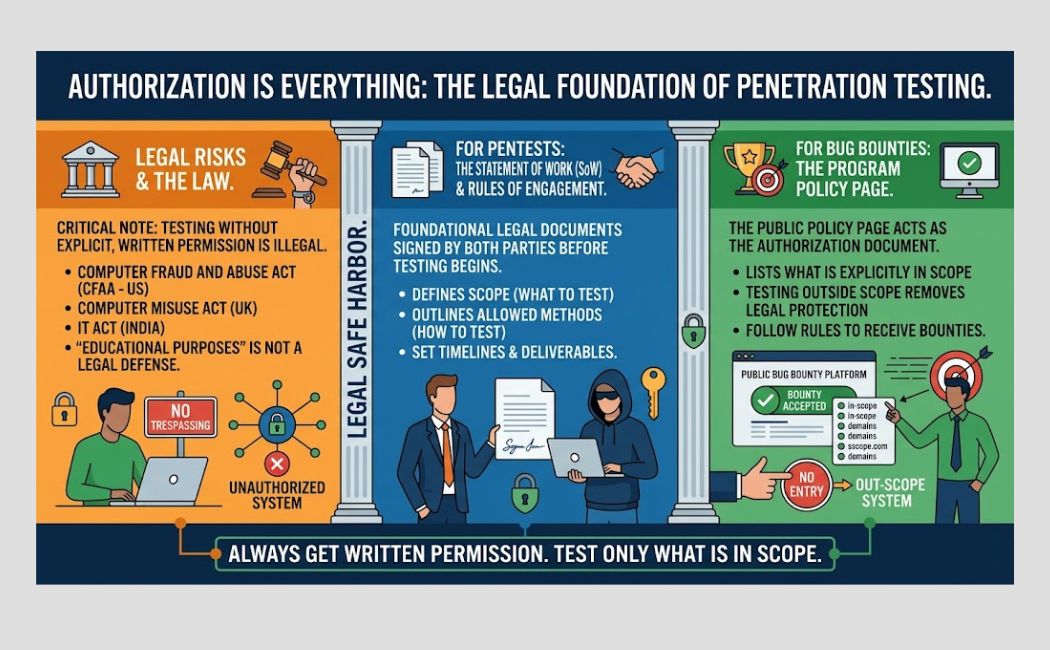
Authorization Is Everything
Performing any penetration testing activity even a single port scan against systems you do not own or have explicit written permission to test is illegal in most jurisdictions (CFAA in the US, Computer Misuse Act in the UK, IT Act in India, etc.). “Educational purposes” is not a legal defense.
Both pentests and bug bounty programs rely on a foundational legal document:
For pentests: a Statement of Work (SoW) and Rules of Engagement signed by both parties before any testing begins.
For bug bounties: the program’s public Policy page on the bounty platform, which acts as the authorization document. Testing only what is explicitly in scope on that page is safe harbor going outside it removes legal protection.
Why SPT Matters in 2026?
As attack surfaces grow cloud, APIs, AI-integrated systems, IoT the structured discipline of a standard penetration testing (SPT) remains the gold standard for understanding real risk. It is not a one-time checkbox; leading organizations pentest continuously, complement this with bug bounties for ongoing researcher coverage, and treat every finding as an opportunity to build a more resilient system.
For security researchers, understanding pentest methodology is the foundation of effective bug bounty hunting. For organizations, it is the difference between assuming you are secure and actually verifying it.
If you are new, undestanding more details Standard Penetration Testing: How You Find and Fix Security Weak Points Fast? .


