What Is Ethical Hacking and How It Protects You from Cyber Attacks? You use the internet every day.
You log in, save your files, and share your personal details. But many people do not realize how easy it is for hackers to break into weak systems.
This is the real problem.
Hence, the full form of “Hacker” is H for Hide IP, A for Aim Victim, C for Crack Encrypt, K for Kill Firewall, E for Enter into the system, and R for Return Anonymous.
Hackers look for small mistakes. A weak password. An old app. A small gap in security. That is all they need to get in. Once inside, they can steal data, damage websites, or even take money.
So, how do you stop this before it happens?
Ethical hacking gives you the answer.
It is a safe and legal way to test your system. You find the weak spots early and fix them before a real attacker can use them. Nothing is harmed. Everything is done with permission.
Think of it like checking your lock before a thief tries your door.
Today, more people want to protect their data, secure their websites, and feel safe online. That is why ethical hacking is now one of the most important parts of cybersecurity.
This guide explains what ethical hacking means, how it works, and how it helps you stay protected in a world full of online risks.

What is Ethical Hacking?
You may hear the word “hacking” and think it is always bad. But that is not true.
Ethical hacking is a safe and legal way to test a system. You check for weak points before a real hacker finds them. You do this with full permission from the owner. This is what makes it “ethical.”
As like you try to open your own door to see if the lock is strong. You are not breaking in. You are making sure no one else can.
When you use ethical hacking, you:
- Find security problems
- Test how strong a system is
- Fix issues before damage happens
Ethical hackers use the same skills as bad hackers. But their goal is very different. They do not steal or harm. They protect your companies, banks, and even governments’ trust in ethical hackers. Help keep systems safe, data protected, and users like you secure online.
Hacking on the ethical side is a legal method of identifying weaknesses in an application, system, or company’s infrastructure and evading security measures to detect possible data security breaches and threats to the network. Accordingly, the full form of;
- H – is for Hacker Hide IP(Internet Protocol),
- A – for Target Victim,
- C – for Crack Encrypt,
- K – for Kill Firewall,
- E – for entering into the system,
- R – for Return Nameless or Anonymous.
Ethical hackers target to search the network or system for vulnerabilities that malicious hackers could take advantage of or take over. They can improve the security footprint to withstand or redirect attacks more effectively.
The owner of the system or network permits cybersecurity experts to conduct such actions to test the system’s security. So, in contrast to malicious hackers, this method is approved, planned, and, most importantly, legally legal.
Ethical hackers looking to examine the network or system for weaknesses that malicious hackers could attack or even cause damage to, collect and analyze information to figure out ways to strengthen the system’s security, network, or applications.
Via this, increase the system’s security footprint to resist or redirect attacks. Companies employ ethical hackers to investigate the weaknesses of their networks and systems and develop solutions to prevent data security breaches.
Informative article: What is the Real Meaning of Ethical Hacking and the Importance of Concepts?
Why Ethical Hacking Is Important Today: Real Problems Face?
You may think hacking only happens to big companies. But that is not true.
Small websites, online shops, and even personal accounts are easy targets. Hackers do not always go for the biggest system. They go for the easiest one.
Here are the real problems you face:
- Weak passwords can be guessed
- Old software can be broken
- Fake emails can trick you
- Open networks can expose your data
These small gaps can lead to big loss. You can lose your data, your money, or even control of your account.
This is why ethical hacking matters.
You test your system before someone else does. You find the weak points early. Then you fix them before any damage happens.
- It is not about waiting for an attack.
- It is about stopping it before it starts.
Today, businesses, websites, and even everyday users rely on ethical hacking to stay safe. It helps build trust, protect data, and keep systems strong in a world where cyber threats are growing every day.
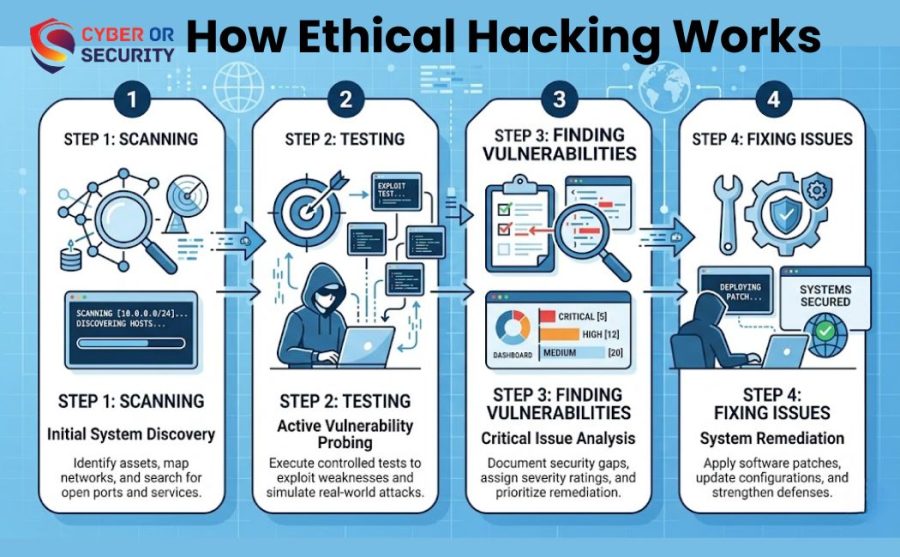
How Ethical Hacking Works: Step-by-Step Simple Process?
You may wonder how ethical hacking actually works. It is not random follows a clear path. You test step by step, just like checking every door and window in a house.
Here is how you do it:
1. Understand the System: First, you learn about the system and check what kind of website, app, or network helps you know where problems might exist.
2. Scan for Weak Points: Next, you look for gaps. These can be weak passwords, outdated software, or open ports. These small issues can become big risks.
3. Try to Enter (Safe Testing): Now you test those weak spots try to enter the system, but safely and legally. This shows how a real attacker might break in.
4. Find and Record Problems: If you get access, you note everything. You write down where the system failed and how it happened.
5. Fix the Issues: This is the most important step. You close the gaps, update systems, and improve security. Now, attackers cannot use those same tricks.
6. Test Again: Finally, you check one more time and make sure everything is secure and working well.
This whole process helps you stay one step ahead of hackers. You do not wait for damage, but prevent it before it happens.
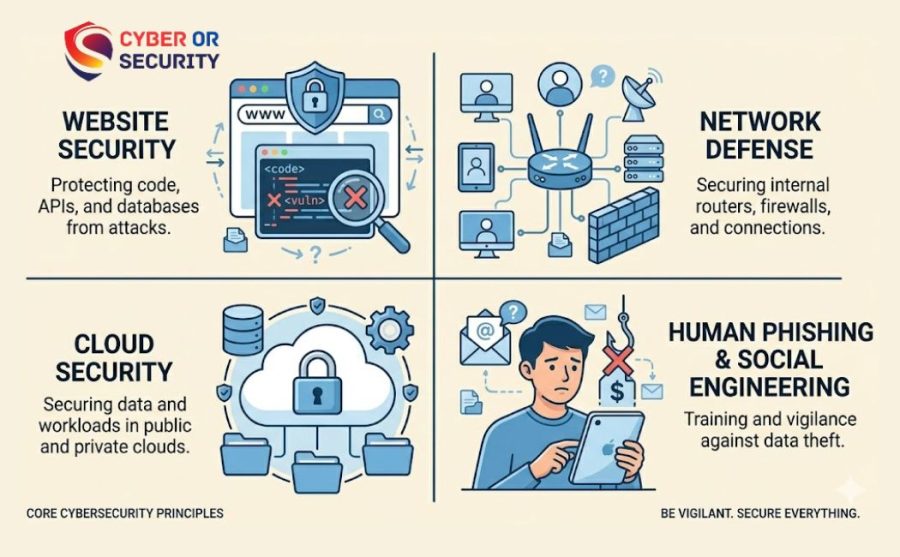
Types of Ethical Hacking Different Ways You Stay Protected
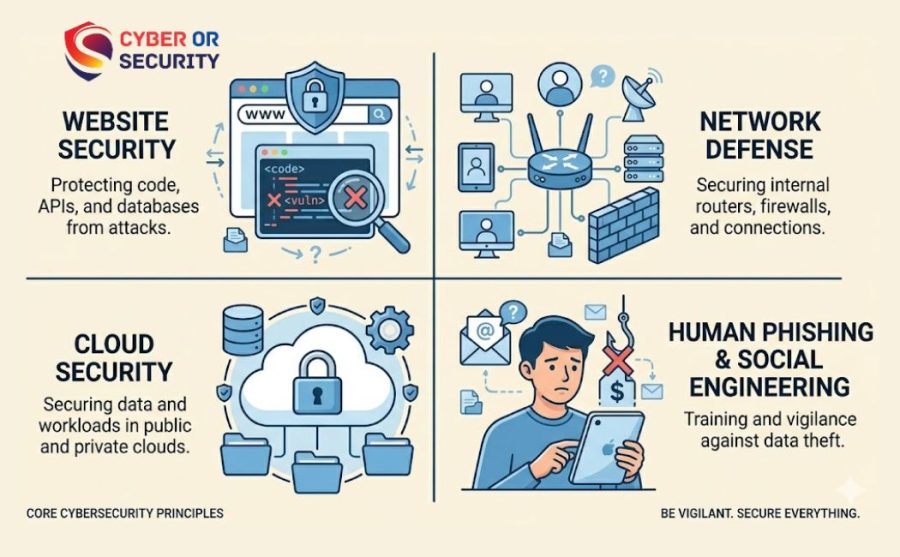
Ethical hacking is not just one thing. You can test many parts of a system. Each type helps you find a different kind of risk.
Here are the main types you should know:
1. Web Application Hacking: You test websites and web apps, and check login pages, forms, and databases.
Goal: Stop attackers from stealing user data or breaking the site
2. Network Hacking: You test networks like Wi-Fi or office systems and check routers, servers, and connections.
Goal: Keep outsiders from entering your network
3. System Hacking: You test computers, laptops, and servers. Also look at operating systems and installed software.
Goal: Protect devices from being taken over
4. Social Engineering: You test human behavior, not just machines and check how people react to fake emails or messages.
Goal: Stop tricks like phishing and scams
5. Wireless Network Hacking: You test Wi-Fi security and check if someone can connect without permission.
Goal: Keep your internet safe from unknown users
6. Cloud Security Testing: Test cloud platforms and online storage. You check how data is stored and accessed.
Goal: Protect online data from leaks or misuse
Each type focuses on a different risk. Together, they give you full protection. You are not just fixing one problem. You are making your whole system strong from every side.
Benefits of Ethical Hacking: How It Helps You Stay Safe?
Now you may ask, why should you care about ethical hacking? The answer is simple. It protects you before something goes wrong.
Here is how it helps you:
1. Protects Your Data: Your data is valuable. Ethical hacking helps you keep it safe from theft or leaks.

2. Stops Attacks Early: You find problems before hackers do. This means attacks can be stopped before they even start.
3. Saves Your Money: A cyber attack can cost a lot. Fixing problems early is always cheaper than fixing damage later.
4. Builds Trust: If your system is secure, people trust you more. This is important for websites, businesses, and online services.
5. Keeps Systems Strong: You keep updating and improving security. This makes your system harder to break.
6. Helps You Stay Ahead: Hackers keep changing their methods. Ethical hacking helps you stay one step ahead of them.
In simple words, ethical hacking is not just about fixing problems. It is about keeping you safe, prepared, and in control.
Five Features of Ethical Hacking Techniques Best Skills and Tools Practices.
Ethical hacking involves identifying vulnerabilities in an organization’s application, system, or infrastructure that an attacker could exploit to achieve access to an individual or an organization. This process stops cybersecurity breaches and cyberattacks by legally hacking systems and identifying weaknesses. A responsible hacker is a person who follows the steps and thinking method that a criminal would follow to gain access to authority and evaluate the security strategies of an organization and its network.
An attacker or ethical hacker will follow the same five-step hacking method to hack into the system or network. Ethical hacking begins with identifying different strategies to hack into systems and exploit vulnerabilities, ensuring constant connection to the system, and finally, removing one’s tracks. Here best five factors of ethical hacking strategies’ impacts on business.
1. Reconnaissance Or Survey With The Art of Ethical Hacking.
The first step on the list of ethical hacking methodologies is scanning or Reconnaissance, usually called the steps of gathering information or footprint with exploration. This preparation phase aims to gather as much information as possible.
Before initiating an attack, the attacker gathers all required information regarding the target person. The information will likely include passwords, meaningful information about employees, etc. An attacker could collect the information using tools like HTTP
Track to download the entire site to collect information about an individual or by using search engines like Maltego to study individuals through websites, profiles of employees, news, and other information.
Reconnaissance Hack for Good: How Ethical Hacking Protects Against Cyber-threats?
Observation is the most critical stage of ethical hacking. A preliminary survey enables you to identify potential attacks and assess the likelihood of an organization’s systems being vulnerable to them. A preliminary survey enables you to identify potential attacks and assess the likelihood of an organization’s systems being vulnerable to them. The preliminary survey or Footprinting process collects data from different fields:
- (Transmission Control Protocol) TCP And (User Datagram Protocol) UDP Services.
- Vulnerabilities
- Through specific IP addresses.
- Host of the network
When it comes to ethical hacking search or footprinting comes in two forms:
- Active Survey: This footprinting method involves gathering data directly from the target using tools like Nmap to look through the target’s network.
- Passive Survey: Another method of footprinting and collecting information is not directly interacting with the person or contacting the target. Hackers or hacking with ethical motives can collect information through Facebook, social media sites, and other websites that are accessible to the public.
2. Scanning: 3 Best Ethical Hacking Processing for Vulnerability Dictations.
The second stage of the hacking process is scanning and analyzing, where hackers try to find various ways to get information about their target. The attacker seeks data like user accounts, credentials, Internet Protocol (IP) Addresses, etc.
Ethical hacking is to find an easy and speedy way to connect to the network and scan for data. Premium and free Kali Linux Tools, like dialers, port scanners, sweepers, network mappers, and vulnerability scanners, are employed to look up records and data during the scanning process. Three different kinds of scanning techniques are used in the ethical hacking process. They are as follows:
- Vulnerability scanning: This scanning technique focuses on the weaknesses and vulnerabilities of the target and explores different ways to exploit these weaknesses. The process is automated using tools like Netsparker, OpenVAS, and Nmap.
- Port Scanning: This is done using port scanners, dialers, and other tools for gathering data or software that listens to the open (Transmission Control Protocol) TCP and UDP (User Datagram Protocol) ports and running live systems, services, and other applications on the targeted host. Penetration testers or attackers utilize the scanning process to identify ways to access an organization’s systems.
- Network Scanning: The technique is utilized to identify active network devices and discover ways to use a network. The network could represent an organizational network with all employees’ systems linked to the same network. Hackers who are ethical use scans of networks to improve the security of a network by identifying weaknesses and opening doors.
3. Gaining Access: Exploring the Role of Ethical Hacking in Cybersecurity Defense.
The next hacking stage is when an attacker uses all means to gain access without authorization to the system or applications. An attacker could employ various methods and tools to gain access to and into an organization.
The hacking stage aims to gain access and exploit the system by downloading malicious software or an application site, along with sensitive data gain, gaining access without authorization, demanding ransom, and so on.
Metasploit is among the most commonly used tools to gain access to the system, and social engineering is one of the most widely used methods to attack an individual.
Ethical hackers and penetration testers can secure entry points, ensure the systems and applications are password-secured, and protect the network infrastructure using firewalls. They may send fake social engineering emails to employees and determine who is most likely to be vulnerable to cyberattacks.
4. Maintaining Access: Impact on Technology and Society.
When the attacker can gain access to the target’s system, they try their best to ensure that they have access. In this phase, the hacker constantly attacks the system, initiates DDoS attacks, uses the compromised system as a launch pad, or even takes over the entire database.
Backdoors and Trojans are programs that attack a system, vulnerable to stealing passwords, essential records, and much more.
In this scenario, the attacker seeks to keep their access unauthorized until they can complete their malicious actions without letting the victim figure it out.
Hackers who are ethical or penetration testers could benefit from this method by examining the entire company’s infrastructure for criminal activities and determining the source of the issue to stop the system from being hacked.
5. Clearing Track: The Evolution of Ethical Hackers.
The final stage of ethical hacking is for hackers to clean their tracks since no hacker wants to be caught. That will ensure that hackers leave no trace or evidence that can be identified. It is essential since ethical hackers must keep their connections in the system and not be detected by the incident response or Forensics team.
This includes editing, corrupting, or deleting logs and registry entries. The attacker can also remove or deinstall applications, folders, and software or ensure the modified files are tracked back to their original state. In the field of ethical hacking, ethical hackers could make use of the following techniques to erase their footprints:
- Reverse HTTP Shells
- Clearing caches and histories to eliminate the footprint of digital information
- Using ICMP (Internet Control Message Protocol) Tunnels
These are the five phases in the CEH hacking method that ethical hackers, also known as penetration testers, can employ to find and pinpoint weaknesses, discover potential opportunities for cyberattacks, and limit security risks to safeguard businesses.
You can obtain an ethical hacking certificate for more information on analyzing and improving security policies and network infrastructure.

Challenges Faced by Ethical Hackers: How Do You Define Ethical Hacking?
An ethical hacker requires an in-depth knowledge of information security to identify the potential threat vectors to operational and business information. Ethical hackers usually demonstrate knowledge acquired through acknowledged industry-specific certifications or university computer science Degree programs and hands-on work on security tools.
Security weaknesses in system configurations that are not secure are based on known and undiscovered flaws in software or hardware and operational weaknesses in processes or technological countermeasures. Security threats that may be caused by malicious hacking comprise distributed attacks of denial-of-service where several computer systems are hacked and redirected to attack a particular target, which could be any resource on the computing network.
An ethically-minded hacker can repeatedly and legitimately attempt to penetrate its computer infrastructure. That includes exploiting known attacks to determine the resilience of an organization’s information security posture.
Ethically ethical hackers use many of the same strategies and methods to test IT security measures, just as their unsavory counterparts and black-hat hackers do. But, instead of exploiting vulnerabilities for financial gain, ethical hackers record information about threats to assist organizations in improving the security of their networks by implementing more vital guidelines, procedures, and tools.
Any business that operates an online network connected to the internet or offers an online service must consider subjecting its operating environments to penetration testing performed by ethical hackers.
Some roles may require or require ethical hacker certification.
It is reported that the US Bureau of Labor Statistics (BLS) states that security professionals in the field of information are expected to grow by 32% over the next decade, which is much more than the average 8% across all occupations.
As the demand for cybersecurity specialists and specialists increases, so does the demand for specific skills, such as those required to hack ethically. A few of the jobs that often require certifications in ethical hacking include:
- Ethical hacker
- Penetration test
- Red Team
- Analysts for malware
- Code auditor

Start with cybersecurity
Are you ready to build work and technical skills for an opportunity in cybersecurity? This Google Cybersecurity Professional Certificate on Coursera can help you start looking for jobs such as security analyst, SOC (security operations center) analyst, and many more.
After completing the course, you’ll get access to an exclusive job site with more than 150 employees looking for entry-level cybersecurity positions and other resources that can assist you during your job search.
What are the Fundamental Principles of Ethical Hacking?
Hacking experts adhere to four fundamental principles of protocol:
- Be Legally Practicable: You must obtain valid approval before logging in or conducting the security evaluation.
- Define the Extent of the Assessment: Define the importance of the review to ensure that the ethical hacker’s work is legal and falls within the boundaries set by the organization.
- Report Vulnerabilities: Notify the organization of any vulnerabilities found during the audit. Offer remediation recommendations to address these vulnerabilities.
- Respect Data Sensitivity: Based on the sensitivity and nature of the data, ethical hackers could be required to sign a non-disclosure agreement along with additional terms and requirements imposed by the analyzed organization.

What Is Ethical Hackers? How do They Differ from Malicious Hackers?
Ethical hackers utilize their knowledge to protect and enhance the security and technology of organizations. They offer an essential service to these companies by identifying weaknesses that could lead to an attack on security.
An ethical hacker will report the discovered vulnerabilities to the company. They also provide recommendations for remediation. When a company’s approval is obtained, the ethical hacker will conduct an additional test to ensure the vulnerabilities are fixed.
Criminals seek unauthorized access to resources (the more secure, the more sensitive) to gain financial gain and personal recognition. Specific malicious hackers alter websites or even crash servers to have fun, cause damage to reputation, and create financial losses. The methods employed and the weaknesses discovered remain unreported. They don’t care about increasing the security of the organization.
What are the Limitations of Ethical Hacking?
- Limitation of area of coverage: Hackers with a moral compass cannot expand beyond a specific area’s boundaries to succeed. It’s also not unreasonable to talk about possible attacks that are out of the scope of your organization.
- Resource limitations: Malicious Hackers need to face the deadlines that ethical hackers typically face. Budget and computing power are other constraints for ethical hackers.
- Methods that are restricted: Some companies require experts to avoid testing situations that could cause servers to fail (e.g., Denial of Service (DoS) attacks).

What You Should Know: Is Ethical Hacking a Good Career?
You may be thinking about your future. Is ethical hacking a good career for you?
Yes. And the reason is simple. Every day, more people and businesses go online. At the same time, cyber attacks keep growing. This means the need for skilled ethical hackers is also growing fast.
1. High Demand Worldwide: Companies need experts who can protect their systems. Banks, websites, apps, and even governments look for these skills. This means more job chances for you
2. Good Salary Potential: Ethical hacking is a skilled job. Because of this, companies are ready to pay well for the right talent.
3. You Solve Real Problems: You are not just working on a computer. You are protecting data, money, and people. Your work has a real impact
4. Always Something New to Learn: Cyber threats keep changing. So you keep learning new tools and methods. This keeps your career exciting
5. You Can Start Step by Step: You do not need to know everything at once. You can start with basics like:
- Networking
- Security concepts
- Simple tools
Then grow slowly with practice
Ethical hacking is not just a job. It is a skill that helps you build a strong future in a world that depends on digital security.
If you enjoy solving problems and thinking like a defender, this path can be right for you.
What Certifications and Skills Does Ethical Hacking Need to Succeed?
An ethical hacker must have many computer-related abilities. They usually specialize and become expert subject matter specialists (SMEs) in a specific subject in ethical hacking. All ethical hackers must have the following:
- Experience in scripting languages.
- Expertise in operating systems.
- An in-depth understanding of the world of networking.
- An established foundation in the concepts of security for information.
A few of the best-known certifications are:
- EC Council: Certified Ethical Hacking Certification
- Offensive Security Certified Professional (OSCP) Certification
- CompTIA Security+
- Cisco’s CCNA Security
- SANS GIAC
Conclusion: What is Ethical Hacking Future and Influence Strategies?
What is Ethical hacking? It’s crucial in safeguarding our digital world by identifying vulnerabilities and strengthening cybersecurity defenses. Ethical hackers are the unsung heroes who use their skills for the greater good, helping organizations stay one step ahead of malicious actors.
By working alongside cybersecurity teams, they ensure that our sensitive information remains secure and protected. As technology advances, the need for ethical hackers will only grow, making their expertise more valuable than ever. Let’s celebrate and support these ethical warriors as they continue to defend our online spaces with integrity and skill!
Helpful article: How Hackers Target Human Cybersecurity Vulnerability Digitally Connected World?
FAQ: Matter of What is Ethical Hacking on Online Platforms?
1. Is Ethical Hacking Legal?
Yes, it is legal. You test systems only when you have permission. Without permission, it becomes illegal.
2. Can a beginner learn ethical hacking?
Yes, you can start as a beginner. You just need to learn the basics step by step, like networking and security.
3. What skills do you need for ethical hacking?
You need simple skills like: Basic computer knowledge. Understanding networks. Problem-solving thinking. You can learn advanced skills later.
4. Do ethical hackers use the same tools as real hackers?
Yes, they often use similar tools. The difference is in the purpose. Ethical hackers use them to protect, not harm.
5. How long does it take to learn ethical hacking?
It depends on your effort. You can learn the basics in a few months. Mastering it takes more time and practice.
6. Is ethical hacking a safe career?
Yes, it is safe if you follow the rules and work legally. You always need permission before testing any system.
7. Why is ethical hacking important today?
Because cyber attacks are growing every day. Ethical hacking helps stop problems before they cause damage.
8. Can ethical hacking protect small websites too?
Yes, it helps all types of systems. Small websites are often easy targets, so protection is very important.


